Agentic AI for Application Management Services
Self-healing application operations that reduce L1/L2 toil and accelerate resolution—without changing where teams work.
The Problem
Modern AMS environments support distributed applications, frequent releases, and increasing user demand—yet incident handling, ticket routing, and root cause resolution remain heavily manual.
Process anomalies are often identified after batch completion, increasing scrap and rework exposure.
Engineers must manually correlate MES, ERP, SCADA, and maintenance data to identify root causes.
Approvals, supplier coordination, and containment decisions lack structured orchestration.
Predictive signals exist but are not operationalized into workflow-driven action.
Audit documentation for quality and regulatory compliance is manually compiled.
Agent Capabilities
Agent Capabilities define how autonomous agents operate within your ITSM ecosystem—classifying incidents, correlating context, executing approved runbooks, and continuously learning from outcomes.
Auto-categorize, prioritize, and reduce ticket noise so queues reflect real work.
Auto-categorize, prioritize, and reduce ticket noise so queues reflect real work.
Auto-categorize, prioritize, and reduce ticket noise so queues reflect real work.
Auto-categorize, prioritize, and reduce ticket noise so queues reflect real work.
Auto-categorize, prioritize, and reduce ticket noise so queues reflect real work.
Works with your AMS toolchain.
Aura connects to your existing ITSM, DevOps, and knowledge systems through tool adapters—so teams don’t change where they work.



Pilot KPIs
We align baseline → target → measured movement during pilot.
L1/L2 workload
MTTR
Reopen Rate
SLA Compliance
RCA Cycle Time
Your KPI
What the agent does
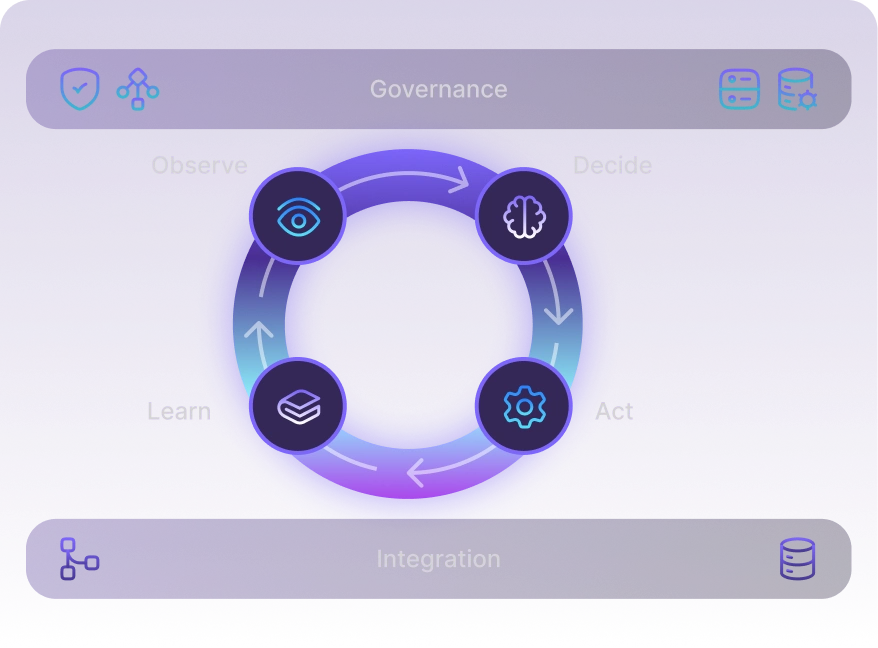
Aura follows a consistent loop—detect, diagnose, act with guardrails, and learn—while updating the ticket with evidence.
Observe → Decide → Act → Learn

Intake
Read the incident + service context (CI, recent changes, similar cases)


Triage
Classify severity/owner, dedupe noise, link related incidents


Diagnose
Propose cause + recommended actions using runbooks/patterns


Approve
Apply risk policy (auto / human approval / block)


Execute & validate
Run approved steps and confirm outcome


Document & learn
Update the ticket, draft RCA notes, create follow-ups

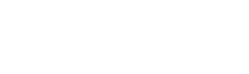
Example Agent actions
- Auto‑resolve Tier‑1 AMS tickets (access, config, known errors)
- Detect recurring failures → open RCA task → propose remediation plan
- Run approved scripts/runbooks → validate outcome → update ticket
Quality & Control
Reference architecture
Observe → Decide → Act → Learn.
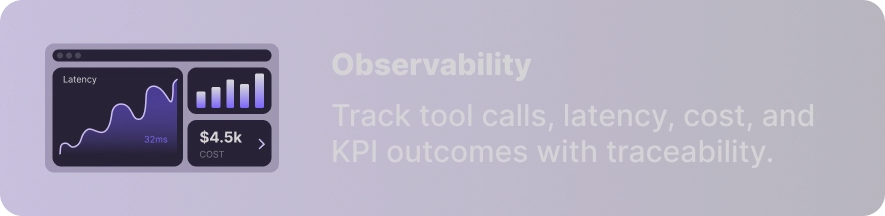
Signals inform decisions, policies constrain actions, and every tool call is tracked—so automation is measurable and auditable.
Signals
Track tool calls, latency, cost, and KPI outcomes with traceability.
Policies
Risk thresholds, approvals, access, and routing rules
Toolbox
ITSM, runbooks, DevOps tools, and knowledge systems
Audit
Evidence, logs, outcomes, and governance reporting
Pilot Plan
Focus on 2–3 high-volume workflows first, then expand based on measured results.








Intake, SLAs, access, and baseline KPI capture
Stand up workflows + smoke tests + critical-path validation
Expand automations + reporting + iteration
Value review (KPI movement + root causes addressed) + scale plan







